Page 57 - 210922_BACnet_Europe-Journal_35_low
P. 57
BACnet Insight
The Practice-Oriented Life Cycle of BACnet/SC
Der praxisorientierte Lebenszyklus von
BACnet/SC
The rapidly growing interconnectivity of building tech- Encrypted communication in building technology The technical implementation of encrypted communi-
nology opens up new opportunities for attackers to cation is associated with challenges. Companies need
manipulate and sabotage, for example, cooling sys- The digital transformation of building technology (OT- a public key infrastructure for this or must expand the
tems for IT and OT rooms. BACnet Secure Connect Building) faces organisations and infrastructure opera- existing IT PKI for building OT. This requires profes-
(BACnet/SC) is a building brick for securing the asso- tors with complex challenges in the area of cyber security sional certificate management to ensure compatibility
ciated complex automation systems and should be (OT-Security). BACnet Secure Connect is developing into with existing systems. Certificate management requires
considered from an operational perspective throug- a crucial technology that systematically closes security a precise strategy for the initial generation, distribution,
hout the entire building life cycle. gaps in building automation and enables encrypted com- revocation and regular renewal of cryptographic keys.
Die rasant wachsende Vernetzung von Gebäudetech- munication for sensitive building technology.
nik eröffnet Angreifern neue Einfallstore zur Manipu- Life cycle of BACnet/SC – from requirement to
lation und Sabotage von bspw. Kälteanlagen für IT & The regulatory landscape is increasingly tightening the certificate
OT-Räume. BACnet Secure Connect (BACnet/SC) ist requirements for the protection of building technology.
ein Baustein für die Absicherung der damit verbunde- The NIS2 Directive and the BSIG require operators of BACnet/SC requires more than just a simple change-
nen, komplexen Automatisierungssysteme und sollte critical infrastructures to implement risk management over from unencrypted to encrypted communication.
vom Betrieb her, über den kompletten Gebäudele- and comply with comprehensive security measures, The process starts with the future operator and user,
benszyklus, mitgedacht werden. while the Cyber Resilience Act (CRA) forces manufactur- who first define the basic security requirements. What
ers of components that can communicate via networks are our specific security objectives (protection needs
to comply with technological security standards, such as assessment)? Which protection mechanisms need to
encryption. be implemented? These strategic considerations form
the foundation for all further steps regarding organisa-
tional and technical protective measures.
Building automation specialists translate these con-
ceptual requirements into a concrete system or net-
work architecture. They develop a comprehensive
certificate strategy that takes into account not only
technical implementation but also long-term security
aspects. How often are certificates exchanged? How
are they managed? These questions are answered iter-
atively with the operator.
Device manufacturers play an important role in the
life cycle, as they already integrate initial security cer-
tificates into their BACnet/SC-enabled devices at the
factory. These pre-installed certificates create an ini-
tial basic level of trust and enable secure transfer and
integrity checks during commissioning.
On site, the contractors/integrators take over further
security measures. They integrate the devices into the
PKI infrastructure and, in consultation with the oper-
ator, replace the initial certificates with organisation-
specific certificates. This enables the consistent and
traceable integration of network-compatible building
technology into a secure building automation system.
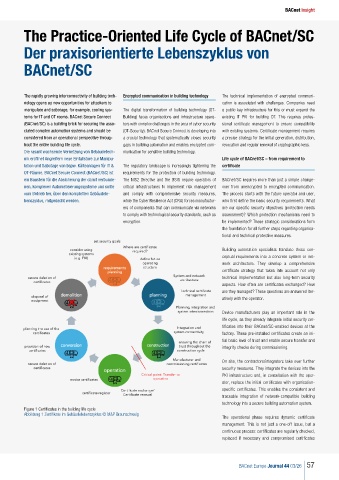
Figure 1 Certificates in the building life cycle
Abbildung 1 Zertifikate im Gebäudelebenszyklus © M&P Braunschweig
The operational phase requires dynamic certificate
management. This is not just a one-off issue, but a
continuous process: certificates are regularly checked,
replaced if necessary and compromised certificates
BACnet Europe Journal 44 03/26 57